The content backend built for your product, not ours
Most CMSes make you fit their model. Sanity lets you define your own. Model content to match your product architecture, automate editorial workflows, and serve every surface from a single structured backend.
Trusted by leading digital innovators
A content backend that scales with your product
Real-time collaboration
Multiple editors can work on the same content simultaneously without conflicts. Changes sync instantly so your team can move fast on product launches, feature announcements, and in-app content updates without stepping on each other.
Flexible content modeling
Define content models in JavaScript or TypeScript to match exactly how your product is built. Your schema lives in code, so it versions, reviews, and deploys like the rest of your codebase. Editors get a tailored Studio interface without any of the complexity.
AI built in, not bolted on
Sanity's structured content backend is what makes AI actually work. Content Agent handles bulk edits and audits through conversation. Agent Context grounds your AI agents in real, governed content. The Agent API generates, transforms, and translates content programmatically. Compute triggers automation on content events.
Extend without limits
Build custom Studio interfaces using the App SDK. Add plugins, connect third-party services, and create content tools your team actually wants to use. When your product grows, your content infrastructure grows with it.
Driving traffic, freeing up engineers, and unleashing content teams
Self serve content creation accelerates content development leading to better SEO and 19% more traffic. Self serve A/B testing boosts conversions.
Applications
- SEO
- Product-led growth
- A/B testing
- Experimentation
Integrations
Marketo


18x
more SEO content
76%
faster site speed
19%
more traffic
Sanity powers content velocity across your team, with ease
From content schema to custom editor in minutes
Define your schema in TypeScript and get a fully functional content workspace instantly. Near-infinitely configurable and customizable interfaces and workflows. The fastest way to get from zero to production-grade content editing.



With Sanity, we can tailor the open-source Studio to meet our content production needs and delight our site visitors, and at the same time, use their Content Lake to host our content. We love the agility and “no-ops happy meal” that Sanity brings to the table. It’s a genius approach.
Content as data without the mess
A fully managed database optimized for content. It connects your content to any system, including ERP, CRM, eCommerce, and AI, giving you ultimate flexibility in how you build and deploy. Query your content as data using GROQ or GraphQL, and Sanity handles the rest.

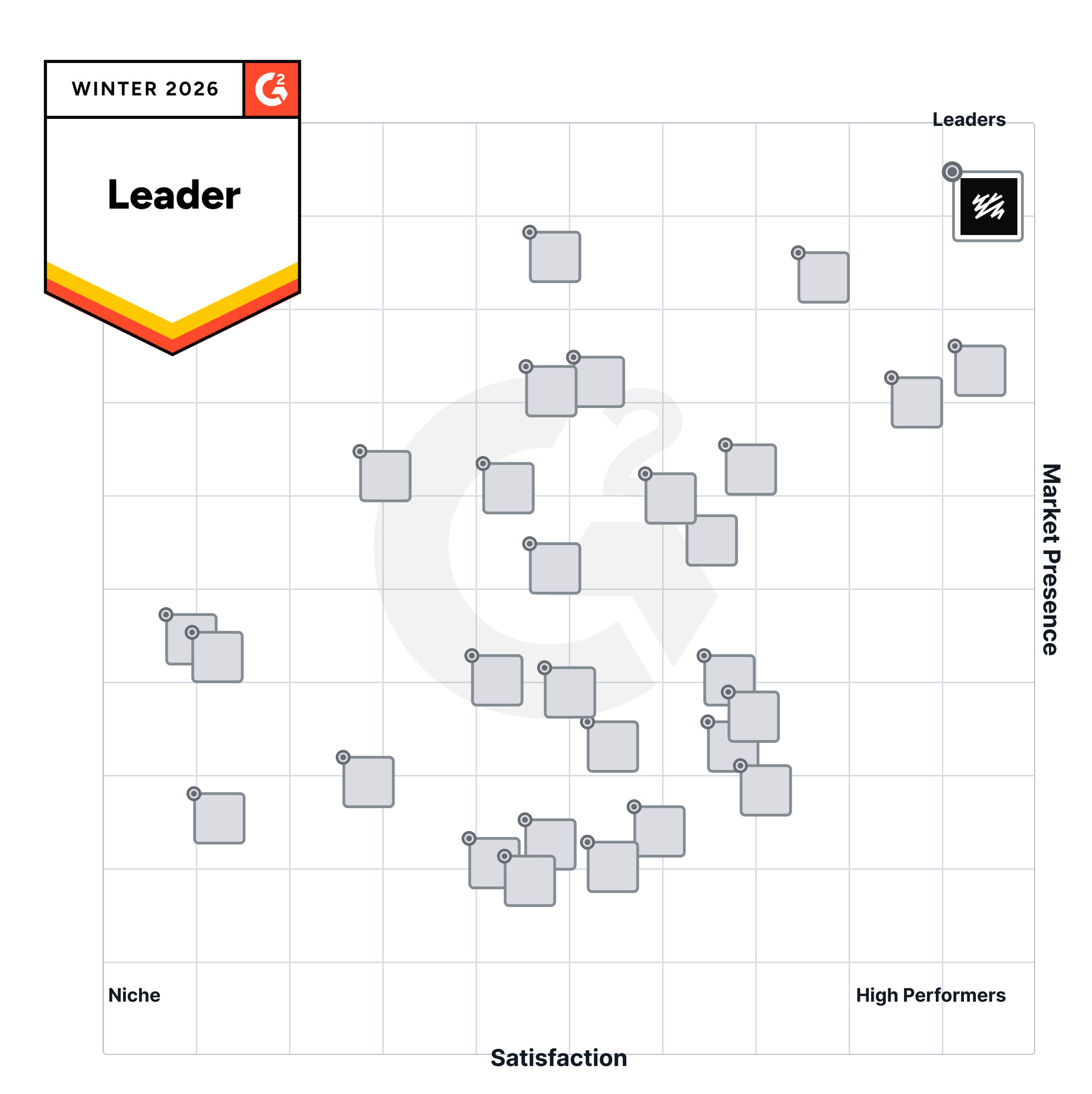
Sanity is ranked #1 out of 85 CMSes on G2
G2.com, the world's largest marketplace for software, has rated Sanity as the #1 leader in the Headless CMS category, as measured by customer review ratings and market presence